ITSM Basics: Know Your Information Security Threats!
Who’s afraid of the big bad wolf? It’s easy to get lost in a sea of IT security noise right now. Not a day, week, or month seems to go by without hearing news of a high-profile data breach, the daily mention of 0-day attacks, or a new advanced persistent threat (APT) with a fancy animal-like name.
So sure, focusing on information security threats related to nation-state attacks is important for many organizations. However, for the general-purpose market, it’s fairly safe to say that your organization isn’t facing attacks from a government-backed team with a multi-million-dollar budget to secretly infiltrate your online shop or marketing website using 0-day attacks and evading any known security defense (well, unless your job is seriously fancier than mine anyway).
What’s more likely to occur is that your website will be defaced, customer data stolen, and your users phished in a “spray and pray” campaign designed to ransom your data or steal your CPU cycles to crypto mine.
Is your head hurting yet? This blog looks at how you can better understand and defend your company against the most likely information security threats.
Employing the Threat Modelling Concept
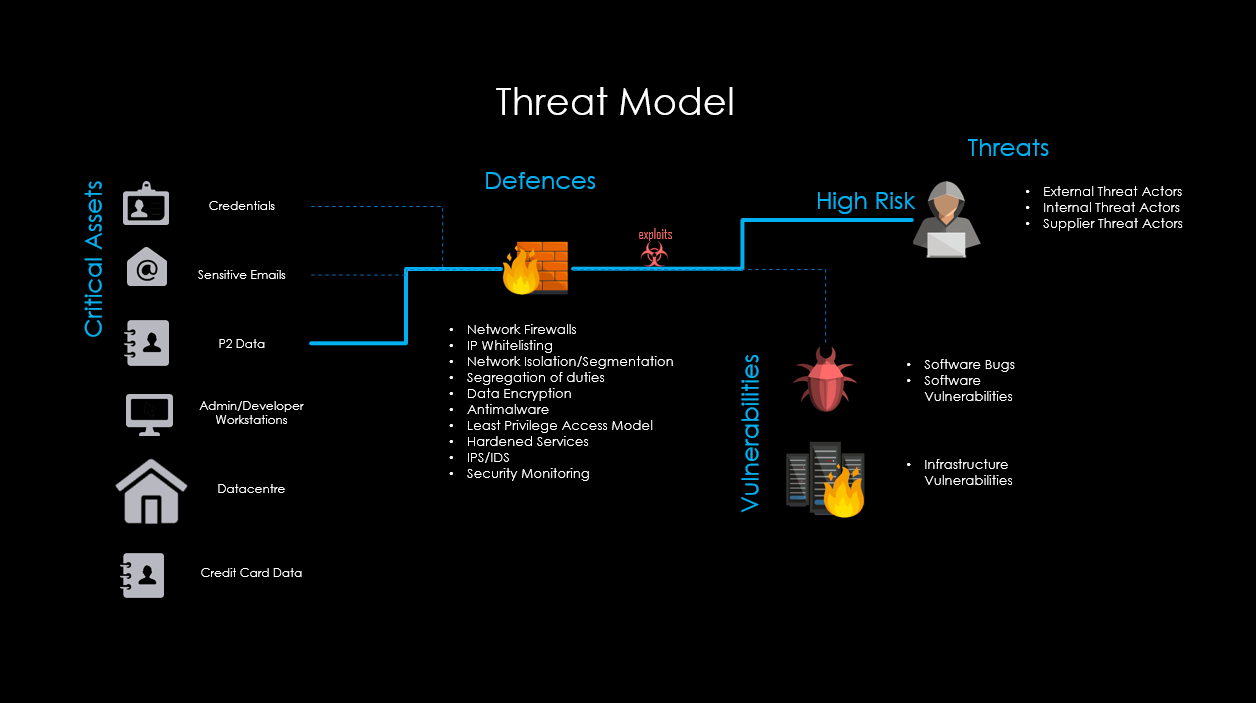
So aside from critical asset identification (which is another rabbit hole in itself), your organization needs to understand what it has, what value this has, and who might attack it. Then how they might attack and what defenses can be put in place to mitigate the likelihood and impact of a security breach.
This is “threat modelling,” and it’s sadly an area where industry security experts see huge gaps within the mid-market and SMB spaces. It’s a real shame because – as well as being a potential business killer – it’s important for organizations to understand the threat landscape and it’s applicably to their business such that they can prioritize their security investments.
The diagram below provides a 10,000-foot view that starts to outline what the organization has (critical assets), what can go wrong (threats and vulnerabilities), and what it’s going to do about them (defenses).
Producing a Threat Model
Creating a threat model generally requires a collaborative approach (threat modelling also isn’t just a point-in-time process). And, fundamentally, the purpose of threat modelling is to help answer the following six questions:
- What are you protecting/building/operating?
- Who might attack it?
- How might they attack it?
- How does the attack realize value for the attacker (or take it away from our business/customers)?
- How is your organization going to prevent, detect, and respond to these threats and vulnerabilities?
- Is your organization being effective in the above?
Producing such a threat model can be put into four phases:
1. Plan
Everything in life seems to require some degree of planning.
To model the current threat landscape, it’s advisable to collect a range of artefacts (i.e. discover) from a number of sources (project management artefacts, system architecture and designs, system operations artefacts, etc.). So, you’ll need to find out who you need to engage with, ensure they’re briefed on why this process is important, and schedule a range of activities (potentially including interviews and workshops); then build your initial plan around this discovery element.
2. Discover
As touched on in the planning section, to create a threat model needs information.
I recommend taking both an evidence-based approach and a collaborative based approach to conducting discovery. Because while evidence gives you hard facts and data that can be worked with, it doesn’t provide context and understanding.
The second reason for recommending a workshop-based approach (a whiteboard session works really well) is that the key point here is to educate and share knowledge within the teams to improve the security of the product, service, or overall operations.
Ultimately, you want people to buy into making not only great quality services but also secure ones.
3. Assess
Once you’ve garnered a good understanding of the service components, information, data flows, processes, and controls you can then start to combine these to outline a range of views which help form the organization’s threat model.
4. Share
It’s important that your threat modelling activities directly contribute to shaping the controls of the service (or wider organization). Regardless of stage, development, or operations, it’s important to get the information into the relevant teams so that the output of the threat modelling process can be used to protect the organization.
Ultimately, whether you’re developing a new product or service or working on securing an existing service (or enterprise), threat modelling helps you to understand the system and assists with the improvement of security posture.
It helps to articulate potential threats and vulnerabilities and helps teams to focus on control prioritization. Think about how you can adapt and integrate threat modelling into your projects and operations to improve security posture and decrease business risk. You’re best to do it now rather than when questions are being asked as to why it wasn’t done (post-breach).
How is the Threat Modelling in Your Organization?
Hopefully your organization is taking its potential information security threats seriously. Or is it one of those ill-prepared mid-market or SMB companies that I referred to earlier? If you don’t know, then find out. And quickly.
Hopefully you found this blog interesting (and interesting enough to check how well threat modelling is being used to defend your company against the most likely information security threats). It might not be your role, but someone has to take responsibility for asking the potentially awkward questions for the sake of everyone.
If you want to know more about threat modelling, or want to share what you know, then please do so in the comments.